I was going to write a post about a completely different topic, but I just got off the phone with my Dad after helping him remove some malware. I’ve decided to share with you what I told him. The situation arose when he got a pop-up advertising the MyPCBackup service and decided it would be a good idea to back up his computer in case something happened. He installed it, paid $40, and then the computer started having problems and couldn’t even connect to the internet. He requested help from their support link and they called him and said his computer was riddled with viruses (without ever having connected to it) and it would cost $200 to fix the problems. Thankfully he said no and called me.
I consider it part of my familial duties to help my family out with computer issues, but I also expect them to follow certain guidelines. At 80 years old and suffering from memory loss, my Dad kind of gets a free pass, but I still reminded him again.
Here are steps you can take to avoid getting malware and spyware on your computer.
What is Malware or Spyware?
It’s kind of a vague definition, but generally it’s software that you don’t want or that does nasty things on your computer. The details vary, from changing your browser’s settings (the homepage, default search engine, etc) without asking for permission or displaying annoying popups advertising something. On the more serious side of the spectrum, it might use your computer to attack other computers as part of a bot net or a DDOS attack, or install a keylogger which lets them intercept your passwords and other sensitive information.
Companies that produce such software make it very hard to get a refund (I suggested my Dad call them to ask for a refund, and if that failed to call his credit card company). They are also shameless spammers.
Rule #1 - If you didn’t ask for it, don’t do it
This is the same rule I live by with door to door salespeople or telemarketers. If I didn’t request the product or service, the answer is no. If you went looking for a backup service and found an ad for it, that’s fine. But if you were just browsing the web and out of nowhere you got a request for you to install a backup service, chances are it’s not reputable.
Only install software that you wanted to install. If they trick you into installing it, uninstall it right away.
Rule #2 - Keep a close eye on the installer
It’s frustrating, but even experienced users have fallen prey to the installer add-on tricks. The way it works is you download software, quite often reputable ones, but during the install process you see confusing and misleading language that’s meant to trick you into installing software addons you don’t want. The reason software publishers agree to this and potentially alienate their users is because they can make money doing it. As a consequence, this is mostly found in free software rather than applications you pay for.
Where possible, I recommend using the portable version of applications. These don’t have installer addons because there isn’t an installer, just a zip file. And there’s the added benefit of being able to put the program in your Dropbox folder where they’re available on any computer with Dropbox installed.
Rule #3 - Establish trust
It’s a good idea to do a quick Google search for the name of the software followed by ‘malware OR spyware OR scam’. If my Dad had done this, he would have seen these results and avoided the software entirely.
You can also look at online reviews, but that can be tricky because you never know if the reviews are legitimate. It’s quite easy on some sites to “stuff the ballot” and make it look like your software has hundreds of positive reviews.
You can also go to sites or ask people you trust. A quick post on Facebook asking if the software you’re about to install is legit could save you a major hassle.
Rule #4 Be wary of attachments
This is true for any attachment, even if it’s from someone you know. The latest trick is to gain access to a user’s email or social media account, then send a message to everyone in their address book asking them to do something, like click on a link. That link will often infect the person’s computer with malware to get it to spread. Sometimes it’s also a way to get access to your own email account, enabling it to start the process over again.
In short, be careful with attachments and strange or unexpected links sent to you by email. Even if the email looks legitimate, it’s safer not to use the link from the email, but to go directly to the web site. That way you know you’re getting to the correct site.
Rule #5 Keep plugins up-to-date
This is mostly for the Adobe Flash and Java plugins and there’s good news. It’s getting easier to keep up-to-date with web browsers like Google Chrome because they take it upon themselves to update the Flash plugin. When you update Chrome itself, it includes the latest Flash updates. This is great, because if you keep Google Chrome updated, you automatically get the latest Flash updates.
If you use another web browser, I recommend running FileHippo’s update checker periodically. It takes a few seconds to scan the installed programs on your computer and tell you what needs to be updated.
Rule #6 Pay attention to the details
If anything seems a little bit odd, raise the red flag and do some research. If something seems too good to be true, it probably is and if there’s anything that gives you any cause for concern, look closely at it before proceeding.
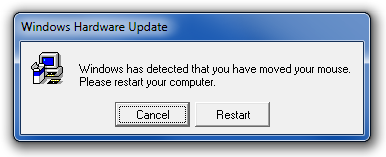
One trick I’ve found helpful is to change the color scheme of the windows. This makes it easier to tell if a popup window is trying to masquerade as a system dialog or if it really is a real dialog. The key is to pay attention to real dialogs so you can tell the difference.
In short, be careful out there. And if you ever come across MyPCBackup asking you to pay $40, you’ll know what to do!